Xefence · CENTRA
Secure Every User, Device,
and Access Path
Unified Identity and Access Security Platform
CENTRA is the unified identity and access security platform from Xefence designed to protect digital identities across modern enterprise environments. As organizations adopt cloud-first architectures, hybrid work models, and distributed applications, identity has become the primary gateway to enterprise systems, and one of the most targeted attack vectors for cyber threats.
Unified Identity Security
Across Your Enterprise
Modern enterprises rely on thousands of identities — employees, contractors, partners, applications, and machines — to access critical business systems. As digital ecosystems expand, identity-based attacks such as credential theft, privilege abuse, and unauthorized access have become one of the leading causes of security breaches.
CENTRA addresses this challenge by delivering a security-focused identity platform that combines authentication, authorization, governance, and behavioral intelligence into a unified framework — continuously evaluating identity risk and integrating with the broader Xefence ecosystem to detect, analyze, and respond to identity-driven threats in real time.

Intelligent Identity & Access Management
CENTRA delivers a unified identity security platform that continuously authenticates users, enforces adaptive access policies, and governs permissions across cloud, on-premise, and hybrid enterprise environments.

Privileged Access & Governance
The platform enforces least-privilege access controls across human and machine identities, providing continuous visibility into entitlements, privilege escalation risks, and policy violations across enterprise systems.

Behavioral Threat Intelligence
Through integration with the broader Xefence ecosystem, CENTRA applies behavioral analytics and real-time threat intelligence to detect anomalous identity activity and respond to identity-driven threats before they escalate.
Real-Time Identity Security
Visibility & Control
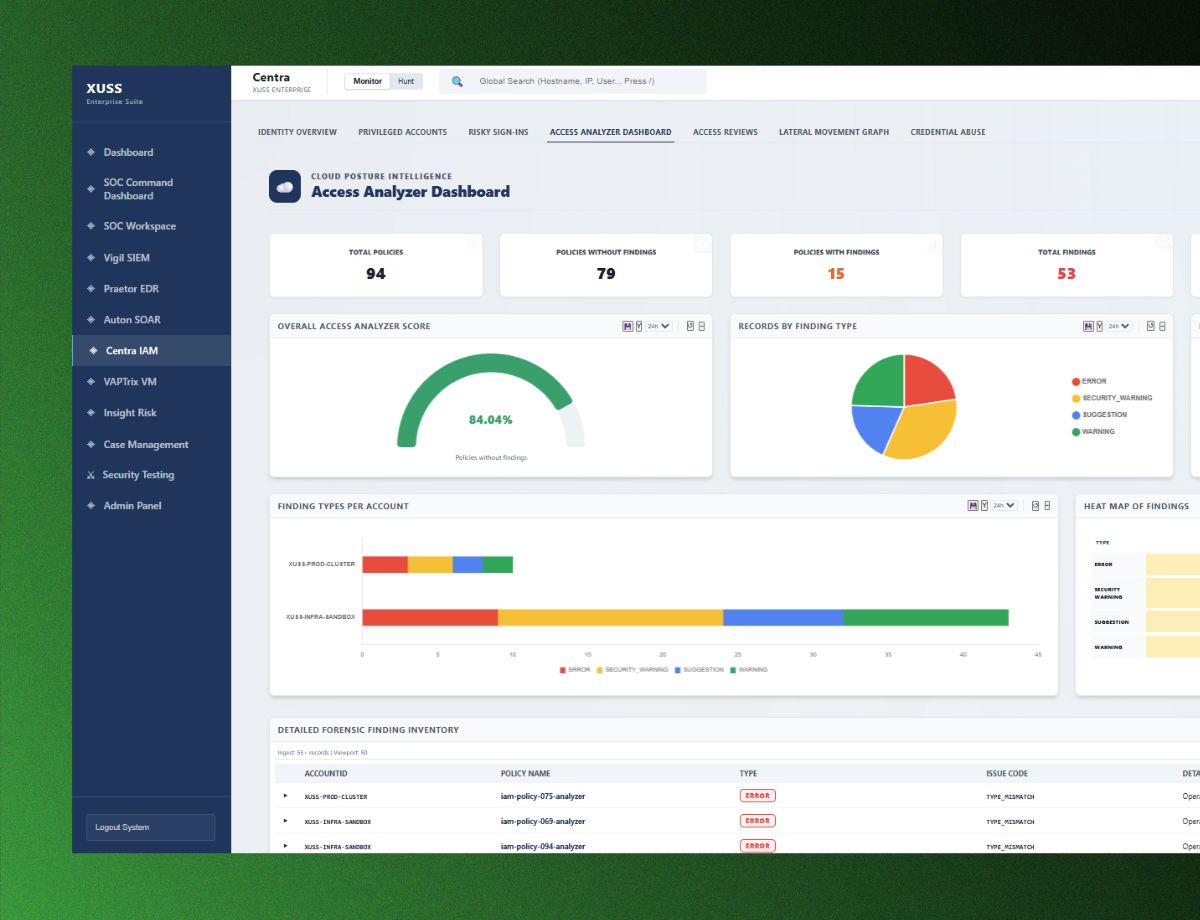
CENTRA provides a modern and intuitive user interface designed for security teams, identity administrators, and IT operations teams.
The platform dashboard offers real-time visibility into authentication activity, identity risk scores, and access policy enforcement across enterprise systems. Security teams can monitor identity security posture, investigate suspicious login activity, and manage identity policies from a centralized console. Role-based dashboards allow CISOs, SOC analysts, and administrators to quickly identify potential identity threats, analyze authentication behavior, and respond to suspicious activity with greater efficiency.
How It Works
How CENTRA
Works
CENTRA operates on a continuous identity trust model that evaluates authentication activity and contextual signals across every access interaction. Instead of relying solely on static login credentials, the platform analyzes multiple contextual factors to determine the legitimacy and risk level of each access request.
Unlike traditional systems that validate identity only at the time of login, CENTRA continuously monitors identity sessions throughout their lifecycle — detecting threats even after authentication has been completed and correlating identity signals with endpoint activity, monitoring data, and vulnerability intelligence across the Xefence ecosystem.
Contextual Signal Analysis
CENTRA analyzes user behavior patterns, device posture, geographic location, session activity, and network context to assess the legitimacy and risk level of every access interaction in real time.
Dynamic Identity Trust Scoring
Each identity interaction is assigned a dynamic trust score based on real-time contextual signals and enterprise risk indicators, enabling the platform to continuously evaluate access legitimacy beyond initial authentication.
Adaptive Access Policy Enforcement
When anomalies are detected, CENTRA automatically enforces adaptive policies — triggering additional authentication, applying privilege restrictions, initiating session verification, or terminating sessions based on the risk level identified.
Continuous Session Monitoring
CENTRA monitors identity sessions throughout their full lifecycle, ensuring trust is maintained during active sessions and correlating identity signals with endpoint and monitoring data across the broader Xefence security ecosystem.
CENTRA protects digital identities through advanced identity security and access control
Identity Intelligence Engine
The Identity Intelligence Engine continuously analyzes authentication events, behavioral patterns, and contextual signals to generate dynamic identity trust scores — enabling security teams to detect abnormal access patterns and identify potential identity threats before they escalate.
Adaptive Access Control
CENTRA enforces context-aware access policies that dynamically adjust authentication requirements and access privileges based on risk levels — ensuring users can access resources securely while preventing unauthorized or suspicious access attempts.
Identity Governance Framework
The platform provides comprehensive visibility into identity privileges, access rights, and access pathways across enterprise systems — enabling security teams to monitor privilege usage, identify excessive permissions, and enforce least-privilege access policies.
Identity Analytics & Monitoring
CENTRA offers advanced analytics and monitoring tools that provide insights into identity activity across the enterprise — enabling security teams to analyze authentication patterns, detect anomalies, and generate detailed reports to strengthen identity security posture.
Unified Identity Visibility Across Your Enterprise Ecosystem
CENTRA integrates seamlessly with enterprise identity ecosystems and security platforms to provide unified identity visibility across the organization.
Enterprise Directory Services
Connects with enterprise directory services such as Active Directory to synchronize identity data, enforce access policies, and monitor authentication activity across the organization.
Cloud Identity Providers & SaaS Applications
Supports integrations with cloud identity providers and SaaS applications to extend identity governance and access control across modern cloud environments.
Endpoint Security & Monitoring Tools
Integrates with endpoint security and monitoring tools to correlate identity activity with device posture and endpoint behavior signals for stronger threat detection.
Security Analytics & SIEM Platforms
Connects with security analytics and SIEM platforms to feed identity intelligence into existing detection and response workflows across the enterprise security stack.
Xefence Platform Ecosystem
Natively integrates with VIGIL, PRAETOR, AUTON, and VAPTrix to correlate identity activity with broader enterprise security signals, strengthening threat detection and response capabilities.
Built for Enterprise
Compliance Readiness
CENTRA provides comprehensive auditing, governance, and monitoring capabilities that support industry security standards and regulatory compliance requirements.
ISO 27001
Information security management systems standard for systematic risk treatment.
SOC 2
Service organization controls for security, availability, and confidentiality.
GDPR
General Data Protection Regulation for data privacy and security compliance.
NIST
NIST cybersecurity framework guidelines for security risk management.
Flexible Deployment for
Every Enterprise
CENTRA offers flexible deployment models to support the security and operational requirements of modern enterprises.
On-Premises Deployment
Ideal for organizations that require full control over identity infrastructure and authentication data within their internal environments.
Full Data ControlHybrid Deployment
Combines on-premises identity systems with cloud-based access control capabilities to support hybrid enterprise architectures.
Balanced FlexibilityCloud Deployment
Provides scalable identity security across distributed environments and cloud-native applications while reducing infrastructure complexity.
Scalable CoverageHow CENTRA Is Built
A scalable and modular architecture designed to support large-scale enterprise environments while ensuring high availability, flexibility, and performance.
The four core architecture layers
Identity Intelligence Layer
Analyzes authentication signals, behavioral patterns, and contextual risk indicators to evaluate identity trust in real time.
Policy Enforcement Layer
Applies contextual access policies across enterprise applications, infrastructure, and services to ensure secure authentication and authorization.
Identity Governance Layer
Provides centralized visibility and control over identity lifecycle management, privilege assignments, and access governance.
Integration Layer
Connects CENTRA with enterprise identity providers, directory services, cloud platforms, and other Xefence security solutions.
Transform Identity into a Security Advantage
Strengthen identity security and enable secure access across modern enterprise environments with CENTRA. Discover how continuous identity trust and adaptive access control can help protect your organization from identity-driven cyber threats.